Tactics, techniques, and procedures (TTPs) form the foundation of modern defense strategies. Unlike indicators of compromise (IOCs), TTPs are more stable, making them a reliable way to identify specific cyber threats. Here are some of the most commonly used techniques, according to ANY.RUN’s Q3 2024 report on malware trends, complete with real-world examples.
Disabling of Windows Event Logging
Tag: insight
-
5 Most Common Malware Techniques in 2024
-
SteelFox and Rhadamanthys Malware Use Copyright Scams, Driver Exploits to Target Victims
An ongoing phishing campaign is employing copyright infringement-related themes to trick victims into downloading a newer version of the Rhadamanthys information stealer since July 2024.
Cybersecurity firm Check Point is tracking the large-scale campaign under the name CopyRh(ight)adamantys. Targeted regions include the United States, Europe, East Asia, and South America.
“The campaign -
China-Aligned MirrorFace Hackers Target EU Diplomats with World Expo 2025 Bait
The China-aligned threat actor known as MirrorFace has been observed targeting a diplomatic organization in the European Union, marking the first time the hacking crew has targeted an organization in the region.
“During this attack, the threat actor used as a lure the upcoming World Expo, which will be held in 2025 in Osaka, Japan,” ESET said in its APT Activity Report for the period April to -
Malicious PyPI Package ‘Fabrice’ Found Stealing AWS Keys from Thousands of Developers
Cybersecurity researchers have discovered a malicious package on the Python Package Index (PyPI) that has racked up thousands of downloads for over three years while stealthily exfiltrating developers’ Amazon Web Services (AWS) credentials.
The package in question is “fabrice,” which typosquats a popular Python library known as “fabric,” which is designed to execute shell commands remotely over -
Cisco Releases Patch for Critical URWB Vulnerability in Industrial Wireless Systems
Cisco has released security updates to address a maximum severity security flaw impacting Ultra-Reliable Wireless Backhaul (URWB) Access Points that could permit unauthenticated, remote attackers to run commands with elevated privileges.
Tracked as CVE-2024-20418 (CVS score: 10.0), the vulnerability has been described as stemming from a lack of input validation to the web-based management -
Canada Orders TikTok to Shut Down Canadian Operations Over Security Concerns
The Canadian government on Wednesday ordered ByteDance-owned TikTok to dissolve its operations in the country, citing national security risks, but stopped short of instituting a ban on the popular video-sharing platform.
“The decision was based on the information and evidence collected over the course of the review and on the advice of Canada’s security and intelligence community and other -
Large eBay malvertising campaign leads to scams
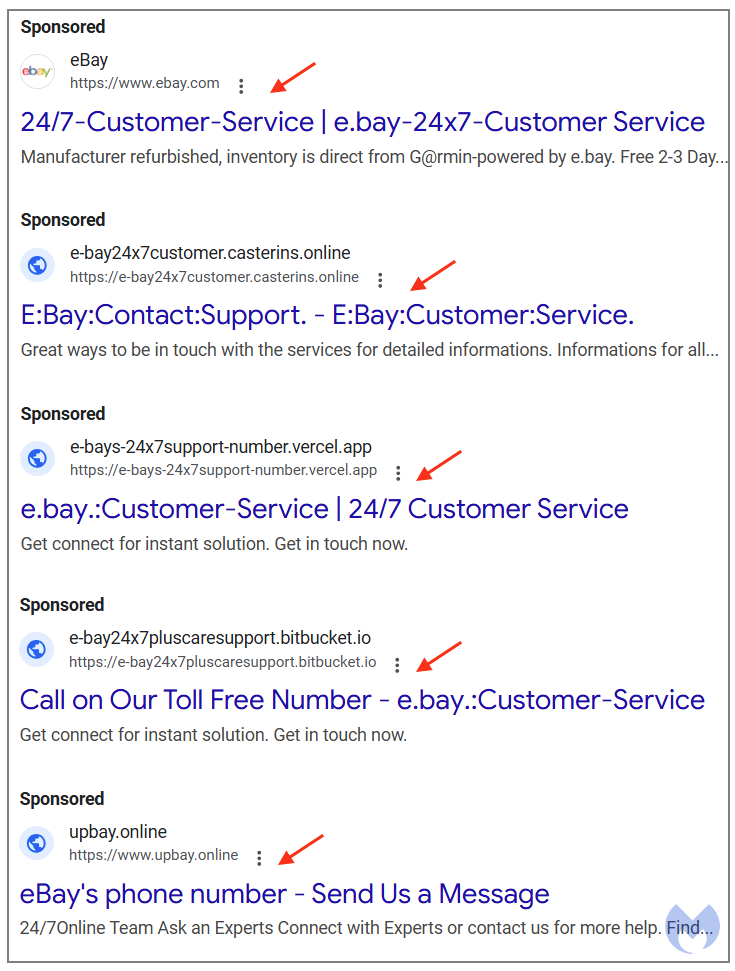
Tech support scammers are targeting eBay customers in the U.S. via fraudulent Google ads. In a few separate searches, we were able to identify multiple Sponsored results that were created from at least four different advertiser accounts.
While most of those ads clearly looked fake, they appeared consistently and prominently enough to trick the inattentive user into a scam. Victims who clicked the ad were redirected to bogus websites prompting them to call for assistance, leading them straight into the scammer’s den.
We have reported the malicious ads to Google and are monitoring for similar campaigns targeting other brands.
Flurry of ads
A search for ‘ebay phone number‘ or ‘ebay customer service‘ from the U.S. using Google Chrome returned several ads that were entirely fraudulent. Upon closer inspection, we found that they were created from four separate advertiser accounts, some belonging to legitimate entities, some created from scratch.
The first ad shown in the screenshot above is the most deceiving of all since it uses eBay’s brand name, logo and website. While Google has strict rules about who may be allowed to do this (i.e. the owner, affiliates), scammers are able to still “comply” with the rule and yet be total crooks.
All they need to do is ensure the final URL (once you click the ad) is one the same domain or is a subdomain that matches the one shown in the ad. That’s the case here, as they are using developer.ebay.com. (part of eBay’s Developers Program Search) which can technically be claimed as belonging to ebay.com.
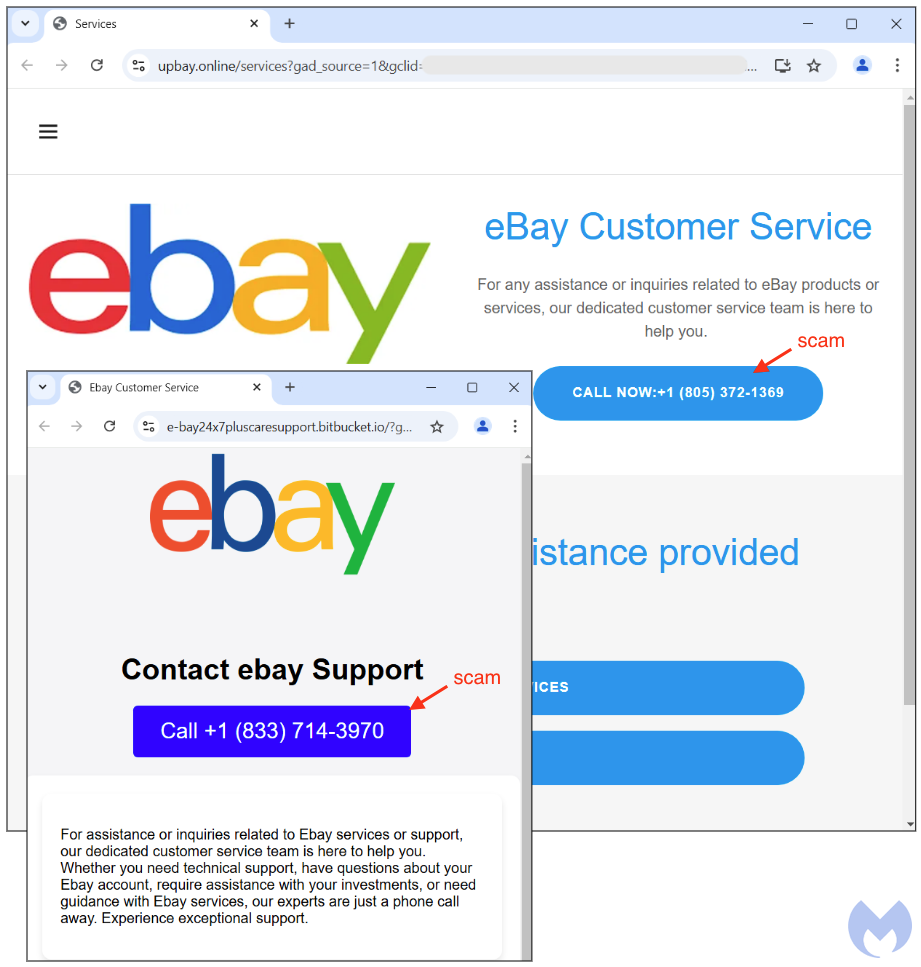
Yet, as you can see below, the destination URL is not what one would expect. It shows a search portal with a printed search result that has eBay’s customer service phone number (narrator: it is not).
This is a trick we’ve seen recently with various online platforms: you perform a calculated search query, even if you know no result will be found. What matters is that your search query will appear on screen, and will be used to fool people who see it. In the example above, the search query was for “eBay.Customer-Service +1 (866) 409[-]9281“.
The other ads redirect to fake websites or pages hosted on cloud providers such as BitBucket claiming to be eBay customer service. Once again, scammers make it clear and obvious that users should call the phone number displayed on screen.
Keeping scammers at bay
Calling any of those phone numbers is strongly discouraged, unless of course your favorite sport is scam baiting. The tried and tested “tech support scam” is one of the most costly type of crime for American consumers.
From call centres mostly located overseas, young people with a broken English accent will attempt to trick victims into giving them access to their computer or phone. The end goal is to steal as much money as they can, by requesting gift cards or by taking over people’s own bank accounts.
It is important to always double check before calling any phone number, especially if it came from an ad or an unsolicited email. In doubt, always visit the source, i.e. ebay.com to access support via live chat or get their official number.
If you weren’t already, you may want to consider using a browser extension such as Malwarebytes Browser Guard. Not only does it block ads, it also detects phishing sites of various kinds.
We don’t just report on threats – we help safeguard your entire digital identity
Cybersecurity risks should never spread beyond a headline. Protect your—and your family’s—personal information by using identity protection.
Indicators of Compromise
Fake pages
e-bays-24x7support-number[.]vercel[.]app
developer[.]ebay[.]com
e-bay24x7pluscaresupport[.]bitbucket[.]io
upbay[.]online
e-bay24x7customer[.]casterins[.]online
e-bay24x7-customers-services-assist[.]onrender[.]comFraudulent phone numbers
1[-]866[-]409[-]9281
1[-]833[-]714[-]3970
1[-]805[-]372[-]1369 -
VEILDrive Attack Exploits Microsoft Services to Evade Detection and Distribute Malware
An ongoing threat campaign dubbed VEILDrive has been observed taking advantage of legitimate services from Microsoft, including Teams, SharePoint, Quick Assist, and OneDrive, as part of its modus operandi.
“Leveraging Microsoft SaaS services — including Teams, SharePoint, Quick Assist, and OneDrive — the attacker exploited the trusted infrastructures of previously compromised organizations to -
New Winos 4.0 Malware Infects Gamers Through Malicious Game Optimization Apps
Cybersecurity researchers are warning that a command-and-control (C&C) framework called Winos is being distributed within gaming-related applications like installation tools, speed boosters, and optimization utilities.
“Winos 4.0 is an advanced malicious framework that offers comprehensive functionality, a stable architecture, and efficient control over numerous online endpoints to execute